最新版 Burp Suite Professional 2024.10 更新於 2024/11/12

Burp Suite 是一個整合平台,針對執行網路應用程式的安全測試。它將各種工具完美結合在一起,以支援整個測試過程,從最基本的測繪(mapping)和應用程式的攻擊面分析,到尋找並藉機利用安全漏洞。Burp 讓你完全掌握、結合日新月異的自動化及先進的手工技術,使你的工作更快、更有效率且更有趣。
Burp Suite 包含以下關鍵組件:
攔截:Burp Proxy 讓你能檢查並修改你的瀏覽器和目標應用程式之間的通訊
應用程式警告:Burp Spider 針對抓取的內容及功能
Web應用程式掃描:Burp Scanner 可自動檢測多元類型的安全漏洞
入侵者工具:Burp Intruder 可執行功能強大的自定攻擊,去找尋且利用不尋常的安全漏洞
中繼器工具:Burp Repeater 可手動修改並補發單獨的HTTP請求,並分析其回應
Burp Sequencer 用於分析應用程式發出的安全關鍵符記的隨機程度
此外它也有能力保存你的工作並在之後恢復
可擴展性:Burp Extender 這項組件則讓你能夠輕鬆編寫自己的插件,在Burp中執行複雜且高度自定義的任務工作
Burp 易於使用且直接,讓新使用者能夠立即開始工作。Burp同時也是高度可配置的軟體,包含了許多強大的功能,來協助最具經驗的測試人員的工作。
*HTTP 訊息編輯器
用於查看並編輯HTTP需求與回應
*儲存及恢復狀態 (Pro版功能)
*搜尋工具
*目標分析
此功能用於分析目標web應用程式,其能告訴你有多少靜態與動態的URL、當中每個需要多少參數
*內容發現
可用於發現"不可見的內容"
*工作排程(Pro版功能)
你可以在規定的時間內,使用任務調度程序自動啟動和停止某些任務
*生成 CSRF PoC(pro版功能)
在特定請求下,可生成proof-of-concept(POC)cross-site request forgery (CSRF)攻擊
*URL-Matching規則
to define URL-based scoping for various functions, such as general Target scope, the scope of individual functions like live scanning, URLs returning streaming responses, and the scope of session handling rules.
*Response Extraction規則
to define the location within a response of a varying item that needs to be extracted.
*記憶設置
在默認情況下,Burp會記住所有的配置選項,即使關閉程式後,也能在下一次運行時恢復。
*手動測試模擬器
*警報
透過各工具所產生的警報有助解決網路連接或其他問題
| Enterprise | Professional |
|
|
V Web漏洞掃描程序 X 預定和重複掃描 X 無限的可擴展性 X CI集成 V 高級手動工具 V 基本的手動工 |
Web vulnerability scanner Enterprise Professional
- Coverage of over 100 generic vulnerabilities, such as SQL injection and cross-site scripting (XSS), with great performance against all vulnerabilities in the OWASP top 10.
- Burp’s cutting-edge web application crawler accurately maps content and functionality, automatically handling sessions, state changes, volatile content, and application logins.
- Burp Scanner includes a full JavaScript analysis engine using a combination of static (SAST) and dynamic (DAST) techniques for detection of security vulnerabilities within client-side JavaScript, such a DOM-based cross-site scripting.
- Burp has pioneered the use of highly innovative out-of-band techniques (OAST) to augment the conventional scanning model. The Burp Collaborator technology allows Burp to detect server-side vulnerabilities that are completely invisible in the application’s external behavior, and even to report vulnerabilities that are triggered asynchronously after scanning has completed.
- The Burp Infiltrator technology can be used to perform interactive application security testing (IAST) by instrumenting target applications to give real-time feedback to Burp Scanner when its payloads reach dangerous APIs within the application.
- Burp’s scanning logic is continually updated with enhancements to ensure it can find the latest vulnerabilities and new edge cases of existing vulnerabilities. In recent years, Burp has been the first scanner to detect novel vulnerabilities pioneered by the Burp research team, including template injection and web cache poisoning.
- All reported vulnerabilities contain detailed custom advisories. These include a full description of the issue, and step-by-step remediation advice. Advisory wording is dynamically generated for each individual issue, with any special features or remediation points accurately described.
Advanced manual tools Professional
- Use Burp project files to save your work incrementally in real-time, and pick up seamlessly where you left off.
- Use the configuration library to quickly launch targeted scans with different settings.
- View real-time feedback of all discovered vulnerabilities on Burp's central dashboard.
- Place manual insertion points at arbitrary locations within requests, to inform the Scanner about non-standard inputs and data formats.
- Use live scanning as you browse to fully control what actions are carried out for what requests.
- Burp can optionally report all reflected and stored inputs, even where no vulnerability has been confirmed, to facilitate manual testing for issues like cross-site scripting.
- You can export beautifully formatted HTML reports of discovered vulnerabilities.
- The CSRF PoC Generator function can be used to generate a proof-of-concept cross-site request forgery (CSRF) attack for a given request.
- The Content Discovery function can be used to discover hidden content and functionality that is not linked from visible content that you can browse to.
- The Target Analyzer function can be used to analyze a target web application and tell you how many static and dynamic URLs it contains, and how many parameters each URL takes.
- Burp Intruder is an advanced tool for automating custom attacks against applications. It can be used for numerous purposes to improve the speed and accuracy of manual testing.
- Intruder captures detailed attack results, with all relevant information about each request and response clearly presented in table form. Captured data includes the payload values and positions, HTTP status code, response timers, cookies, number of redirections, and the results of any configured grep or data extraction settings.
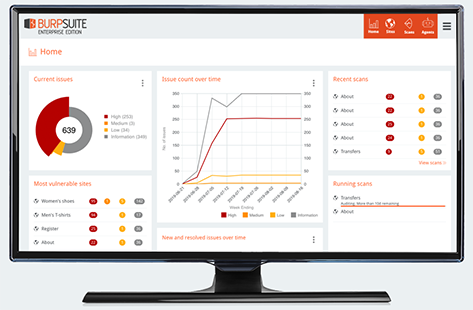
Scheduled and repeat scans Enterprise
- Burp Suite Enterprise Edition can perform scheduled scans at specific times, or carry out one-off scans on demand.
- You can configure repeat scans to run indefinitely or until a defined end point.
- You can view in a single place the entire scan history for a given web site.
Unlimited scalability Enterprise
- Burp Suite Enterprise Edition has extreme scalability, and can scan indefinitely many web sites in parallel.
- You can configure all of your organization's web sites in one place, organized to reflect your organizational structure.
- All scan results are aggregated in one place, providing an at-a-glance view of your organization’s security posture
- The scalable agent pool distributes workload across multiple machines, allowing your deployment to grow to any size, and perform as many parallel scans as your organization requires.
- Burp Suite Enterprise Edition supports multiple users with role-based access control (RBAC) to restrict access to sensitive data. There are no licensing restrictions on the number of users.
CI integration Enterprise
- Bring security automation forward in your development lifecycle using Burp's CI integration.
- Automatically launch vulnerability scans from your CI system via the REST API.
- There are ready-made native CI plugins for popular platforms such as Jenkins and TeamCity, and a generic CI driver that can be easily installed in any CI system.
- You can run scans per commit, on a schedule, or as part of your deployment pipelines.
- The CI integration can be configured to break software builds based on the severity of discovered issues.
Essential manual tools Professional
- Burp Proxy allows manual testers to intercept all requests and responses between the browser and the target application, even when HTTPS is being used.
- You can view, edit or drop individual messages to manipulate the server-side or client-side components of the application.
- The Proxy history records full details of all requests and responses passing through the Proxy.
- You can annotate individual items with comments and colored highlights, letting you mark interesting items for manual follow-up later.
- Burp Proxy can perform various automatic modification of responses to facilitate testing. For example, you can unhide hidden form fields, enable disabled form fields, and remove JavaScript form validation.
- You can use match and replace rules to automatically apply custom modifications to requests and responses passing through the Proxy. You can create rules that operate on message headers and body, request parameters, or the URL file path.
- Burp helps eliminate browser security warnings that can occur when intercepting HTTPS connections. On installation, Burp generates a unique CA certificate that you can install in your browser. Host certificates are then generated for each domain that you visit, signed by the trusted CA certificate.
- Burp supports invisible proxying for non-proxy-aware clients, enabling the testing of non-standard user agents such as thick client applications and some mobile applications.
- HTML5 WebSockets messages are intercepted and logged to a separate history, in the same way as regular HTTP messages.
- You can configure fine-grained interception rules that control precisely which messages are intercepted, letting you focus on the most interesting interactions.
- The target site map shows all of the content that has been discovered in sites being tested. Content is presented in a tree view that corresponds to the sites’ URL structure. Selecting branches or nodes within the tree shows a listing of individual items, with full details including requests and responses where available.
- All requests and responses are displayed in a feature-rich HTTP message editor. This provides numerous views into the underlying message to assist in analyzing and modifying its contents.
- Individual requests and responses can be easily sent between Burp tools to support all kinds of manual testing workflows.
- The Repeater tool lets you manually edit and reissue individual requests, with a full history of requests and responses.
- The Sequencer tool is used for statistical analysis of session tokens using standard cryptographic tests for randomness.
- The Decoder tool lets you convert data between common encoding schemes and formats used on the modern web.
- The Clickbandit tool generates working clickjacking attacks against vulnerable application functions.
- The Comparer tool performs a visual diff between pairs of requests and responses or other interesting data.
- You can create custom session handling rules to deal with particular situations. Session handling rules can automatically log in, detect and recover invalid sessions, and fetch valid CSRF tokens.
- The powerful Burp Extender API allows extensions to customize Burp’s behavior and integrate with other tools. Common use cases for Burp extensions include modifying HTTP requests and responses on the fly, customizing the Burp UI, adding custom Scanner checks, and accessing key runtime information including crawl and scan results.
- The BApp Store is a repository of ready-to-use extensions contributed by the Burp user community. These can be installed with a single click from within the Burp UI.
Professional
Burp Suite system requirements
The system requirements for Burp Suite are largely dependent on your intended use for the software. While you can generally perform most tasks on a relatively low-spec machine, some use cases (for example, running multiple scans concurrently) may require significantly more power to run without a noticeable effect on performance.
CPU cores / memory
» Minimum: 2x cores, 4GB RAM - This spec is suitable for basic tasks such as proxying web traffic and simple Intruder attacks. While Burp Suite may run on a machine with a lower specification than this, we do not recommend doing so for performance reasons.
» Recommended: 2x cores, 16GB RAM - This is a good general-purpose spec.
» Advanced: 4x cores, 32GB RAM - This spec is suitable for more intensive tasks, such as complex Intruder attacks or large automated scans.
Free disk space
» Basic installation: 1GB
» Per project file: 2GB
Note:
While 2GB is the recommended minimum free disk space for a project, note that project files can get significantly larger than this (potentially up to many tens of GB), depending on factors such as the amount of proxy history included, the number of scans run, and the number of Repeater tabs open.
Operating system and architecture
Burp Suite supports the latest versions of of the following operating systems:
» Windows (Intel 64-bit)
» Linux (Intel 64-bit)
» OS X (Intel 64-bit and Apple M1)
Enterprise
Burp Suite Enterprise Edition system requirements
The system requirements for Burp Suite Enterprise Edition depend on several factors:
» The number of concurrent scans you want to run.
» The applications you want to scan.
» The number of issues expected.
» The number of active Burp Suite Enterprise Edition users in your installation.
The system requirements that we recommend provide satisfactory performance for most use cases. However, you may need to use infrastructure with a higher specification to meet your particular needs.
For the best performance, we recommend you distribute scans across multiple scanning machines. If you need help with the system requirements, please email our support team.
The system requirements are specific to the type of deployment you choose. To learn more about the types of deployment available, see Deployment options.
For a production deployment, we recommend that you configure an external database.
System requirements
Please see the following pages for the system requirements for your deployment type, and the external database:
» Standard deployment (on-premise or cloud-hosted virtual machines).
» Kubernetes deployment.
» External database (recommended for all deployment types).
Concurrent scans
When you determine your system requirements, you need to consider the number of concurrent scans that you plan to run. In Burp Suite Enterprise Edition, concurrent scans are the number of scans that you want to run at the same time. The links above explain how concurrent scans change your system requirements.
